How the Repository of Practices was built
The 11 best practices featured in this Repository are the result of a structured research and validation process carried out by Université Libre de Bruxelles (ULB) in the framework of COcyber Work Package 4, Task 4.1. The full details are documented in Deliverable D4.1 — Guidelines on cybersecurity civil-defence cooperation. This page offers a web-friendly summary.
The methodology was designed to answer four research questions:
- What types of structured cooperation currently exist between the civilian and defence cybersecurity communities in the EU?
- What characteristics make a cybersecurity cooperation practice effective, scalable, and transferable across different EU Member States?
- What barriers and enablers influence the success of civil-defence collaboration in cybersecurity?
- Which critical gaps remain in the coordination between the two communities, and how can practical examples address them?
A three-step process
The research followed a rigorous three-step design aimed at identifying, evaluating and validating impactful cooperation practices.
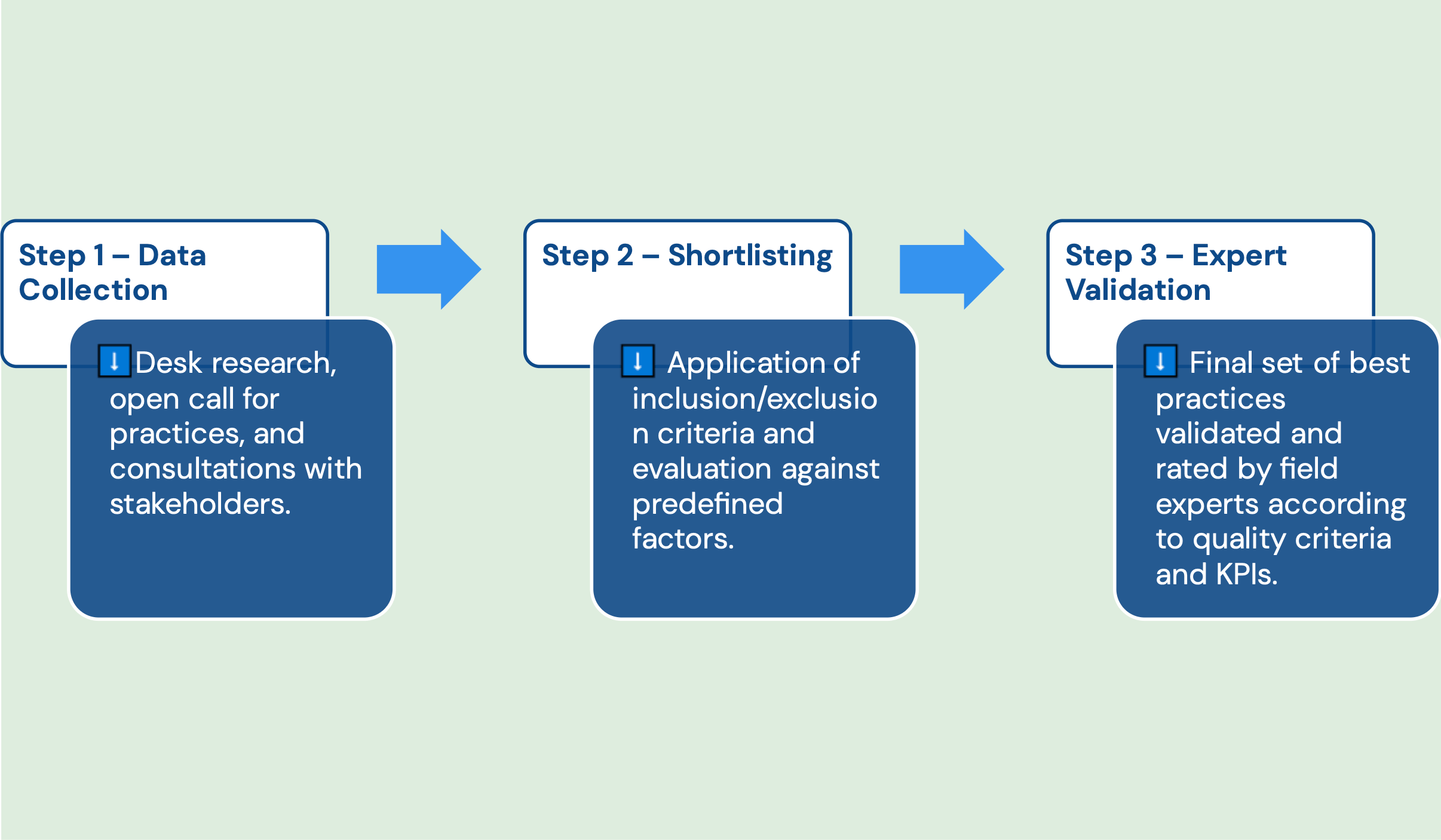
Step 1 — Data collection
The first step built a comprehensive Long List of practices, ensuring wide coverage of national, European and non-European initiatives relevant to the European context.
The ULB team reviewed over 600 sources, including ENISA and EDA reports, EU cybersecurity frameworks, NATO publications, academic literature and policy analyses. Each source was assessed for its relevance to civil-defence cybersecurity cooperation.
In parallel, an open call for practices invited organisations to submit their own cooperation initiatives, and targeted stakeholder consultations were conducted with cybersecurity and digital-resilience specialists from industry, academia, public institutions and policy advisory bodies. Consulted organisations included, among others, NRD Cyber Security, CYEN, EOS, the National Technical University of Athens, the National University of Public Service, the Central Bank of Hungary, CEA France, The Lisbon Council and Aegis Research EU.
This combined effort enriched the dataset with lesser-known and context-specific initiatives that would have been missed through desk research alone.
Step 2 — Shortlisting
The Long List was then filtered down to a shortlist of 20 practices by applying a set of predefined inclusion criteria:
- Relevance — the practice directly addresses cybersecurity challenges in civilian or defence sectors.
- Effectiveness — documented success in mitigating threats, improving resilience or enhancing coordination.
- Scalability — potential for adaptation across different regions, organisations or sectors.
- Collaboration — the practice encourages cross-sector cooperation between civilian and defence entities.
- Evidence-based — supported by case studies, data or expert validation.
- Geographic and temporal scope — practices implemented within the EU27 or associated countries from 2015 onwards.
- Innovation — introduction of new technologies, methodologies or approaches.
- Risk mitigation — ability to address known cybersecurity risks.
- Ethical considerations — including privacy and data-protection implications.
Keyword mapping and content clustering were also applied to detect overlaps and unique features, and to align each candidate practice with the 32 strategic actions identified in Deliverable D2.2, creating a thematic bridge between the needs assessment and the repository.
Step 3 — Expert validation
The shortlisting of the 20 practices followed a two-step validation approach. First, the practices were shared with a panel of domain experts from both civilian and defence backgrounds during a dedicated online consultation event, ‘Best Practice Validation: Cybersecurity and Civil-Defence Cooperation in the EU’, where volunteer experts reviewed the practices and submitted their rankings. In parallel, each practice was independently assessed by two paid experts using the same evaluation matrix. The evaluations from both the volunteer and paid experts were then combined to produce the final validation results. All practices were assessed using a shared evaluation matrix built on seven criteria:
- Feasibility
- Impact
- Efficiency
- Scalability
- Innovation
- Risk mitigation
- Ethical considerations
Scores were compiled on a 1-to-5 scale and aggregated into a ranking by Total Points and Average Points. The 11 highest-ranking practices were retained and constitute the final Repository.
This quantitative selection process was designed to ensure:
- Transparency — scoring based on predefined and documented criteria.
- Comparability — consistent scoring across all practices.
- Robustness — expert-based validation reducing bias.
Linking practices to needs
Each of the 11 best practices in the Repository is tagged with the cooperation needs it addresses, drawn from the needs assessment in Deliverable D2.2. The eight needs are:
- Fragmentation of cybersecurity efforts
- Lack of (or limited) information-sharing
- Lack of awareness capacity
- Lack of dual-use technologies
- Lack of coordinated cybersecurity policies
- Lack of cross-pollination of ideas and best practices
- Lack of cutting-edge innovation
- Cultural differences between the two sectors
This tagging allows users of the Repository to browse practices by the specific cooperation gap they want to address.
Scope and limitations
The Repository focuses on practices implemented within the EU27 and associated countries after 2015. It is not an exhaustive inventory of every cooperation initiative in existence, but a curated selection validated for relevance, transferability and operational soundness. Practices that could not be substantiated with public evidence or expert testimony were not retained, even when promising in principle.
Citing this work
If you reference the methodology or the practices, please cite the source deliverables:
Université Libre de Bruxelles. (2025). Deliverable 4.1. Guidelines on cybersecurity civil-defence cooperation (V.1). Zenodo. https://doi.org/10.5281/zenodo.17293138
Université Libre de Bruxelles. (2025). Deliverable 2.2. Bridging Gaps: A Raw Needs Assessment Report for Enhanced Collaboration Between Civilian and Defence Cybersecurity Spheres (v3). Zenodo. https://doi.org/10.5281/zenodo.16760899
Both deliverables are published under a Creative Commons Attribution 4.0 International licence.